
Our Black and Decker coffeemaker stopped working. The clock was fine. When we pressed the ON button, there was the usual “click” sound, but the coffee simply didn’t brew. Nothing got hot. Okay, let’s open it up to see what’s wrong.




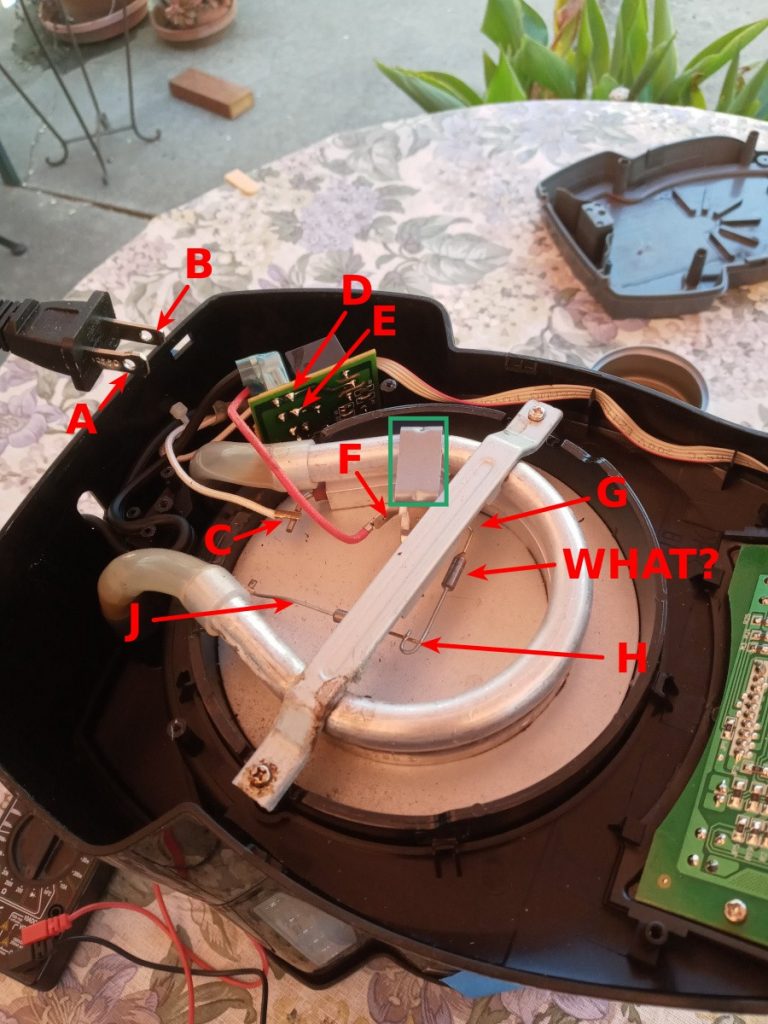
A, the neutral side of the line, connects to the white wire at C.
B, the hot side of the line, connects to D.
D is connected by relay contacts to F. It measured open circuit when the appliance was unplugged.
F goes through a component, probably a thermostat, to G. The DVM showed open circuit between F and G.
G goes through a mystery component to H. The resistance of the component is nil, and is the same both ways, so it’s not a semiconductor. It could be a thermal fuse to open the circuit in case of fire, if the thermostat doesn’t do its job. Between H and J is what appears to be the same thing. If they are fuses, why two of them? Legal issue? Maybe they’re some kind of thermistor to lower power consumption once the pot is brewed, and just being kept warm?
C to J is the heater element, 36 Ω when measured cold.
All of the above I was able to determine without plugging the unit into the wall.
I was hoping for a fixable failure mode, like a loose wire. Or, if the relay contacts had burned out, I could buy a new relay. Or, if one of the thermal fuses opened up, I could bypass it. If the heater element or thermostat failed, those would be too custom to find replacements for. And no, I’m not going to bypass the thermostat. If it were an emergency situation like war or a disaster, I’d do it, but it would be a fire hazard.
Conclusion: It’s not worth fixing. Is there anything worth salvaging? Yes, the carafe and coffee filter. Electronically, there’s a nice relay that I would have kept in the old days. But not anymore. I took it to Goodwill for electronic recycling.